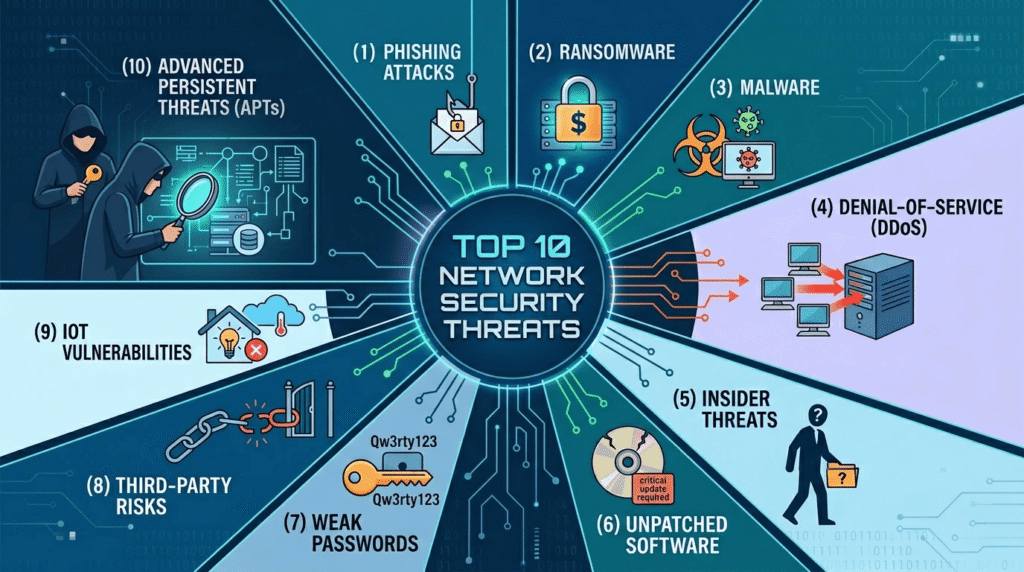
Network security Threats stands at the forefront of modern business resilience, yet many organizations continue to underestimate the sophistication and frequency of today’s cyber threats. This blog examines the ten most pressing security challenges that businesses across every industry are actively navigating not as distant possibilities, but as daily operational realities.
Today’s Network Security Threats range from socially engineered phishing campaigns to patient, undetected advanced persistent intrusions. The attack landscape has grown broader and increasingly calculated. Modern Network Security Threats exploit human behavior, third-party trust, unpatched infrastructure, and poorly secured connected devices no longer depending solely on technical expertise to gain unauthorized organizational access.
What makes this resource particularly valuable is its direct focus on Network Security Threats through a practical lens. Each danger is examined with clarity how it operates, why it succeeds, and where organizational defenses consistently break down. Whether you are a business leader shaping protection investment decisions or a technology professional building resilient security frameworks, understanding these vulnerabilities remains the essential first step.
Awareness alone does not guarantee protection, but it is the foundation upon which every effective security strategy is built.
Why Network Security Has Become a Non-Negotiable Business Priority in Today’s Digital Economy
Network security used to be an IT problem. Leadership signed budgets, asked occasional questions, and moved on. That separation has quietly collapsed.
The contributing factors are clear. Regulatory frameworks around data privacy have grown considerably stricter across global markets. Consumers increasingly weigh a company’s trustworthiness before committing to purchasing decisions. And when a security incident actually unfolds whether it involves ransomware, stolen records, or complete system lockouts the financial repercussions stretch far beyond the initial disruption. Operational downtime, digital forensic investigations, mounting legal expenses, and forfeited business relationships all follow. Countless mid-sized organizations have collapsed entirely beneath that cumulative weight.
Network security today is not a technical checkbox. It feeds directly into whether a business stays operational or does not. The ten threats below are what professionals are dealing with right now.
The 10 Threats You Need to Know About
Before getting into specifics, it helps to understand that network security threats today come from multiple directions simultaneously. Some exploit technical flaws. Others manipulate people. Many combine both. The businesses that handle this well are not necessarily the ones with the biggest budgets they are the ones that understand what they are dealing with.
Spear Phishing Targets Specific Victims Behind Every Major Breach
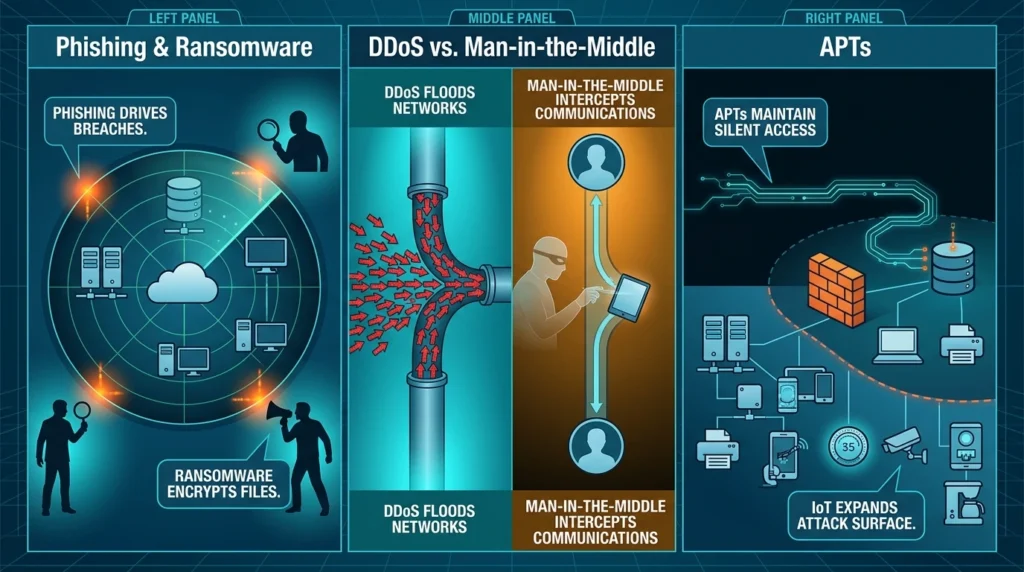
Phishing drives more breaches than most businesses realize. Bulk campaigns still circulate, but spear phishing built around a specific target is where the real network security damage happens today.
- Emails impersonate trusted sources: banks, vendors, internal leadership
- Links redirect to fake login pages built to harvest credentials
- Attachments carry malware that executes silently on opening
- Business Email Compromise (BEC) involves impersonating executives to authorize fraudulent transfers
- Even technically sophisticated employees get deceived the writing quality alone no longer signals risk
Ransomware Encrypts Business Files Before Security Teams Can Respond
Few threats have torn through business operations quite like ransomware. Once inside, it moves quietly across systems, encrypting files faster than most network security teams can respond often before anyone realizes something is wrong.
- Entry points include phishing emails, exposed remote desktop protocols, and unpatched systems
- Lateral movement through a network can happen in hours
- Double-extortion tactics involve stealing data before encrypting it paying the ransom does not guarantee silence
- Recovery costs frequently exceed the ransom itself
- Critical sectors including healthcare and municipal governments are frequently targeted
Malicious and Negligent Insiders Both Compromise Organizational Security
Not every threat originates outside the organization. Insider threats are among the most difficult to detect precisely because the activity often looks like normal, authorized behavior.
- Malicious insiders usually disgruntled employees can delete, steal, or leak sensitive data deliberately
- Negligent insiders create exposure without any harmful intent, through poor password hygiene or mishandling devices
- Third-party contractors with network access represent an extension of this risk
- Overpermissioned accounts make the damage worse when an insider acts
- Behavioral analytics tools exist specifically to detect unusual internal activity patterns
DDoS Floods Networks Until Customer Services Become Unreachable
A distributed denial of service attack floods a network or server with traffic until it becomes unreachable. For any business with customer-facing digital services, this creates immediate, visible damage. Network security teams need active monitoring and mitigation plans for this type of attack specifically because they can materialize with almost no warning.
- Botnets large networks of compromised devices generate the volume
- Amplification techniques multiply the attack traffic significantly
- Outages lasting even a few hours cause measurable revenue loss
- DDoS attacks are sometimes used to distract security teams while a deeper intrusion occurs
- Mitigation typically requires traffic filtering at the network edge or through a CDN provider
Man-in-the-Middle Attacks Secretly Intercept Sensitive Business Communications
When an attacker secretly intercepts communication between two parties without either side knowing that is a man-in-the-middle attack. Protecting network security on endpoints and in transit is the primary defense, and it matters most wherever sensitive data moves.
- Public Wi-Fi is a frequent environment for these attacks
- Attackers can intercept login credentials, session tokens, and financial transactions
- SSL stripping degrades encrypted HTTPS connections to unencrypted HTTP
- Session hijacking allows the attacker to take over an authenticated session
- Certificate validation failures are often how these attacks first become detectable
SQL Injection Exploits Unvalidated Input to Compromise Databases
SQL injection has been exploitable for decades and still causes serious damage. Why? Because developers keep shipping applications without validating user input properly. That single oversight opens the door. Network security breaks down at the application layer more often than most teams expect
- Malicious code slips through form fields, search boxes, or URL parameters
- Databases execute the injected query without questioning it
- Attackers read, alter, or wipe entire databases
- Customer records, passwords, and payment details are frequent targets
- Prepared statements and input sanitization shut this down reliably when actually applied
Zero-Day Exploits Leave Security Teams Completely Without Patches
A zero-day vulnerability is one the software vendor does not yet know about. There is no patch. No advisory. Detection depends entirely on behavioral signals rather than known signatures. For network security operations teams, zero-days represent a genuine blind spot.
- Exploits are discovered and often sold on dark web markets before vendors are aware
- Nation-state actors use zero-days for espionage and long-term access
- Detection requires anomaly-based monitoring rather than signature-based tools
- The window between discovery and patching once a vulnerability becomes public is extremely narrow
- Threat intelligence subscriptions help organizations respond faster when zero-days emerge
Advanced Persistent Threats Maintain Silent Access for Extended Periods
Advanced persistent threats differ from most attacks in their patience. The goal is not immediate damage it is sustained, undetected access. Attackers stay inside a network for months, sometimes years, slowly gathering intelligence or positioning for a larger action. Network security monitoring with behavioral baselines is essential for catching APTs because traditional perimeter defenses rarely flag them.
- APT actors are usually organized groups with significant resources and specific objectives
- They move carefully through a network, avoiding triggers that would alert detection systems
- Data exfiltration happens gradually to avoid creating unusual traffic spikes
- Multiple persistence mechanisms are established to survive partial remediation
- Threat hunting proactive searching for signs of compromise is the primary detection method
Supply Chain Attacks Compromise Thousands Through One Vulnerable Vendor
Supply chain attacks target the software, hardware, or services a business relies on from third parties. One compromised vendor can introduce vulnerabilities into thousands of organizations downstream without any of them making a direct security mistake.
- The trust relationship businesses have with vendors is the core vulnerability being exploited
- Hardware tampering at the manufacturing or logistics stage is a less common but documented risk
- Vendor security assessments and software bill of materials (SBOM) frameworks reduce exposure
- Monitoring for unexpected changes in trusted software behavior is a key detection signal
IoT Device Vulnerabilities Expand Business Network Attack Surfaces Considerably
Connected devices cameras, printers, environmental sensors, smart building systems have expanded the attack surface of most business networks considerably. Many were deployed quickly without much security consideration, and they sit largely unmanaged for years afterward.
- Default factory credentials are rarely changed and are publicly documented
- Firmware update cycles are infrequent or entirely absent for many devices
- Compromised devices serve as quiet entry points into broader network segments
- IoT hardware is frequently recruited into botnets for DDoS campaigns
- Network segmentation isolating IoT devices from core business systems significantly limits what an attacker can reach from a compromised device
Defend, Monitor, and Recover Effectively
These Network Security Threats are not theoretical scenarios constructed to generate unnecessary alarm. Every danger outlined across this list has inflicted real, documented harm on actual organizations worldwide. The encouraging reality is that most Network Security Threats remain manageable through disciplined cybersecurity effort updating systems regularly, restricting access tightly, educating staff thoroughly, and maintaining continuous activity monitoring. No single protective measure addresses every vulnerability. Layered defenses, applied with deliberate precision, ultimately determine whether a business rebounds quickly or fails to recover at all.
