Session Hijacking vs Phishing represents two critical cyber threats that confuse many security professionals and everyday users alike. In an era where data breaches cost businesses millions annually, distinguishing Session Hijacking vs Phishing becomes essential for robust defense. Attackers exploit these techniques to steal access or sensitive information, often leading to financial losses and reputational damage as highlighted in recent cybersecurity reports. Understanding this helps organizations prioritize defenses effectively. This post breaks down their definitions, core mechanisms, key differences, real-world impacts, and prevention strategies to empower you with actionable insights.
What is Session Hijacking?
Session hijacking occurs when cybercriminals intercept and take control of an active user session between a client and a server, often after legitimate authentication. This stealthy attack bypasses initial login credentials by stealing session identifiers like cookies or tokens.
- Attackers commonly use cookie theft, where they snag session cookies transmitted over unsecured networks, allowing them to impersonate users on banking sites.
- Session prediction involves guessing valid session IDs based on patterns in poorly randomized tokens, a vulnerability noted in older web applications.
- Man-in-the-middle (MitM) techniques position attackers between user and server, capturing session data during transmission without HTTPS protection.
- Real-world example: The 2023 Verizon DBIR reported session hijacking in 15% of web app breaches, often via public Wi-Fi exploits.
- Risks escalate with sidejacking, where tools like Firesheep demonstrated easy cookie interception on unencrypted HTTP sessions.
- Tokens become prime targets too, as flawed implementations in APIs enable replay attacks post-capture.
These methods thrive on active sessions, making timing crucial for success.
What is Phishing?
Phishing tricks users into revealing sensitive information or clicking malicious links through deceptive communications mimicking trusted entities. Unlike direct technical exploits, it relies on human psychology via social engineering.
- Email phishing floods inboxes with fake alerts from banks, urging credential entry on spoofed sites that harvest logins.
- Spear phishing targets individuals with personalized lures, such as executive imposters requesting wire transfers, as seen in 2024 OWASP reports.
- Vishing extends to voice calls, where scammers pose as tech support to extract multi-factor authentication (MFA) codes.
- Smishing uses SMS for urgent delivery notifications linking to malware-laden pages.
- Statistics from Verizon DBIR 2024 show phishing in 36% of breaches, underscoring its prevalence over technical hijacks.
- Credential theft dominates outcomes, feeding into larger attacks like account takeovers.
Phishing’s success hinges on urgency and trust manipulation.
Session Hijacking vs Phishing: Core Mechanisms
Session Hijacking vs Phishing differs fundamentally in approach: hijacking seizes existing authenticated sessions, while phishing deceives for initial access. These mechanisms highlight why Session Hijacking vs Phishing demands tailored countermeasures.
- Session hijacking starts post-login, intercepting cookies or tokens via MitM on networks lacking HTTPS encryption.
- Phishing begins with bait, like fraudulent emails directing to fake SMTP servers mimicking legitimate ones.
- Hijackers predict or steal session IDs in real-time, replaying them without user interaction.
- Phishers engineer lures exploiting trust, harvesting credentials for later use.
- OWASP notes session hijacking often chains with cross-site scripting (XSS), unlike phishing’s standalone social vectors.
- Both can involve endpoint compromises, but hijacking targets active traffic, phishing preys on inaction.
Contrasting these reveals hijacking’s technical precision against phishing’s broad deception.
Key Differences in Session Hijacking vs Phishing
Session Hijacking vs Phishing shares goals like unauthorized access but diverges in execution, detection, and impact. Recognizing these distinctions sharpens threat modeling.
- Targets: Hijacking focuses on active sessions via cookies and tokens; phishing aims at credentials through social engineering.
- Detection: Hijacking evades easy spotting without traffic monitoring; phishing triggers via suspicious emails or anomalous logins.
- Impact: Hijacking grants immediate control, risking data exfiltration; phishing enables broader campaigns like ransomware deployment.
- Attack vector: Technical network interception for hijacking versus psychological manipulation in phishing.
- Duration: Hijacking exploits short-lived sessions; phishing builds long-term credential databases.
- Verizon DBIR emphasizes hijacking’s subtlety in web apps versus phishing’s high-volume noise.
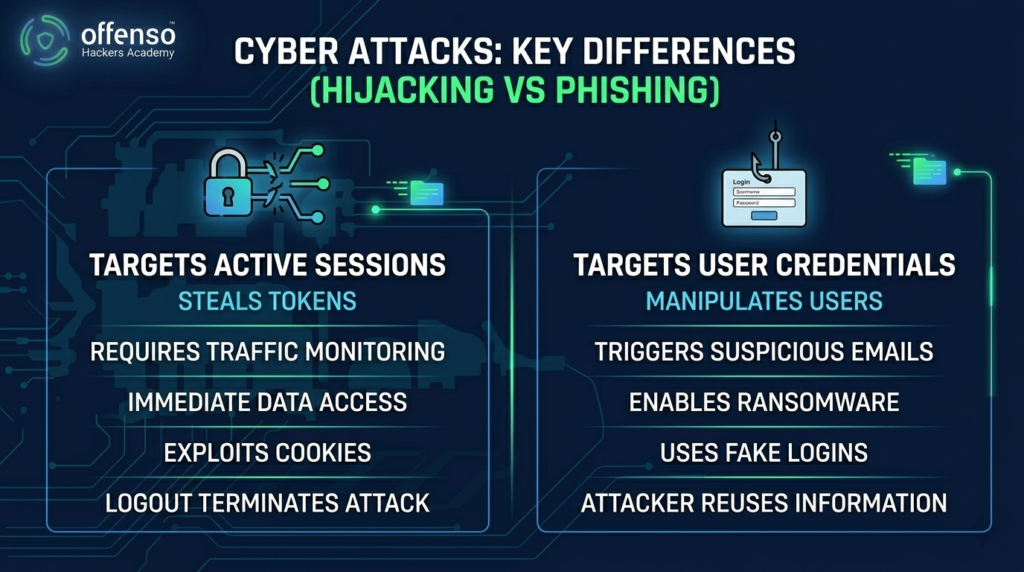
These contrasts guide prioritized defenses.
Real-World Impacts of Session Hijacking vs Phishing
Session Hijacking vs Phishing has inflicted massive damages, from financial theft to operational disruptions. Reports like Verizon DBIR quantify their toll across industries.
Cybercriminals leveraging session hijacking drained accounts in the 2022 Capital One incident variant, where stolen tokens accessed cloud resources undetected. Phishing fueled the 2023 MGM Resorts breach, costing $100 million through vishing-enabled credential grabs. Businesses face regulatory fines under GDPR for hijacking exposures, while phishing erodes customer trust via identity theft. Productivity plummets as IT teams scramble post-incident. OWASP highlights session hijacking’s role in API abuses, amplifying supply chain risks. Collectively, these threats underscore the need for layered protections.
Prevention Strategies
Preventing Session Hijacking vs Phishing requires proactive measures blending technology and user education. Implement these universally applicable tactics to fortify defenses.
- Enforce HTTPS everywhere to encrypt session cookies and tokens, thwarting MitM interception.
- Deploy multi-factor authentication (MFA) that issues short-lived tokens, complicating hijacking replays.
- Use firewalls and web application firewalls (WAFs) to inspect traffic for anomalous session patterns.
- Train teams on phishing red flags like unsolicited requests, reducing click-through rates by 70% per Verizon stats.
- Regenerate session IDs frequently and bind them to IP addresses for added hijacking resistance.
- Enable endpoint protection with anti-phishing browser extensions blocking malicious domains.
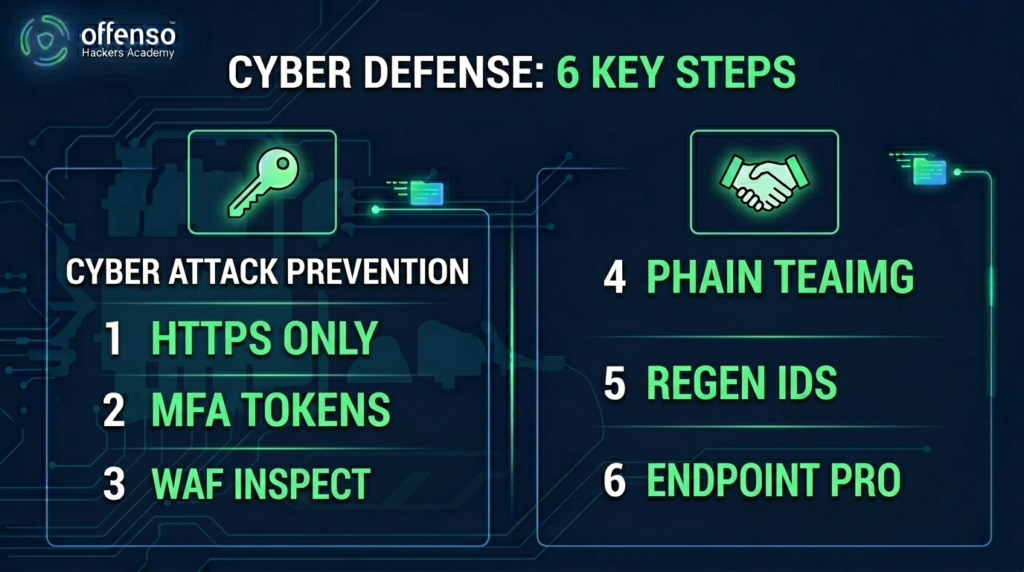
Consistent application minimizes Session Hijacking vs Phishing risks effectively.
Advanced Detection Tactics
Beyond basics, advanced detection elevates response against Session Hijacking vs Phishing. Leverage analytics and automation for early warnings.
Security teams monitor logs for session anomalies, like logins from unusual geolocations despite IP binding. Behavioral analytics flag rapid token usage spikes indicative of hijacking. Email gateways scan for phishing signatures using AI-driven sandboxing. User and entity behavior analytics (UEBA) baselines normal activity, alerting on deviations. Integrate SIEM tools linking SMTP anomalies to potential vishing chains. Regular penetration testing simulates Session Hijacking vs Phishing, refining detection thresholds.
These tactics transform reactive security into predictive resilience.
Conclusion
Distinguishing Session Hijacking vs Phishing equips you to counter both deception and technical exploits effectively. Session hijacking stealthily commandeers active sessions through cookies, tokens, and MitM, demanding encryption and monitoring. Phishing, conversely, manipulates via emails, calls, and texts for credential theft, countered by education and gateways. Their differences in mechanisms, targets, and impacts—from Verizon DBIR-documented breaches to OWASP vulnerabilities highlight tailored defenses like MFA, HTTPS, and firewalls. By grasping Session Hijacking vs Phishing nuances, organizations build topical authority in cybersecurity. Stay vigilant: audit your sessions, train your team, and deploy layered protections today. Your proactive stance could prevent the next costly breach.
