Introduction
Web security threats evolve constantly, but some vulnerabilities refuse to disappear. SQL injection attacks have persisted as one of the most dangerous and exploited web application weaknesses for over two decades. Despite widespread awareness, improved frameworks, and better developer education, thousands of websites continue to fall victim every year. From small business portals to enterprise-grade platforms, no application is immune if proper protections are absent. Understanding how these attacks operate, why they remain relevant, and how to prevent them is no longer optional it is a professional responsibility for every developer, security engineer, and system administrator.

What SQL Injection Attacks Actually Are
At their core, SQL injection attacks occur when malicious input is inserted into a database query, tricking the server into executing unintended commands. Instead of treating user input as plain data, a vulnerable application passes it directly to the database engine without sanitization.
- An attacker enters crafted input into a login form, search bar, or URL parameter
- The input modifies the intended query structure
- The database, whether MySQL, PostgreSQL, or Microsoft SQL Server, executes the manipulated query
- The attacker gains unauthorized data access, authentication bypass, or even system control
Why These SQL Injection Attacks Remain on the OWASP Top 10
The Open Web Application Security Project (OWASP) consistently ranks injection flaws among the most critical risks in web application security. The reason is simple: the attack surface is enormous and the consequences are severe.
- Legacy codebases with unparameterized queries remain in production
- Rapid development cycles often deprioritize security reviews
- Third-party plugins and libraries introduce overlooked vulnerabilities
- Developers confuse input validation with proper query parameterization
- Misconfigured databases amplify the damage once access is gained
How SQL Injection Attacks Identify Vulnerable Targets
Before launching SQL injection attacks, adversaries use reconnaissance techniques and automated tools to probe applications for weaknesses. Burp Suite is among the most widely used platforms for this purpose, enabling testers and attackers alike to intercept and manipulate HTTP requests.
- Automated scanners submit payloads like ‘ OR ‘1’=’1 to test input fields
- Error messages from poorly configured servers reveal database structures
- Burp Suite’s scanner module actively crawls and tests endpoints
- Time-based blind injection tests slow query responses to confirm vulnerabilities
- Search engine dorking identifies exposed admin panels or login pages
The Three Most Exploited SQL Injection Attacks Techniques
Not all injection methods work the same way. Understanding the primary techniques helps organizations prioritize their defenses effectively.
- Classic (In-band) Injection: The attacker retrieves data directly through the same channel used to inject the payload, common in MySQL and Microsoft SQL Server environments
- Blind Injection: No visible error output is returned, so attackers infer database behavior through true/false questions or time delays
- Out-of-band Injection: Data is exfiltrated through a different channel such as DNS or HTTP requests, often used when in-band methods are unreliable
Real-World Impact on Businesses and Users
The damage caused by SQL injection attacks extends far beyond technical disruption. Organizations face legal, financial, and reputational consequences that can take years to overcome.
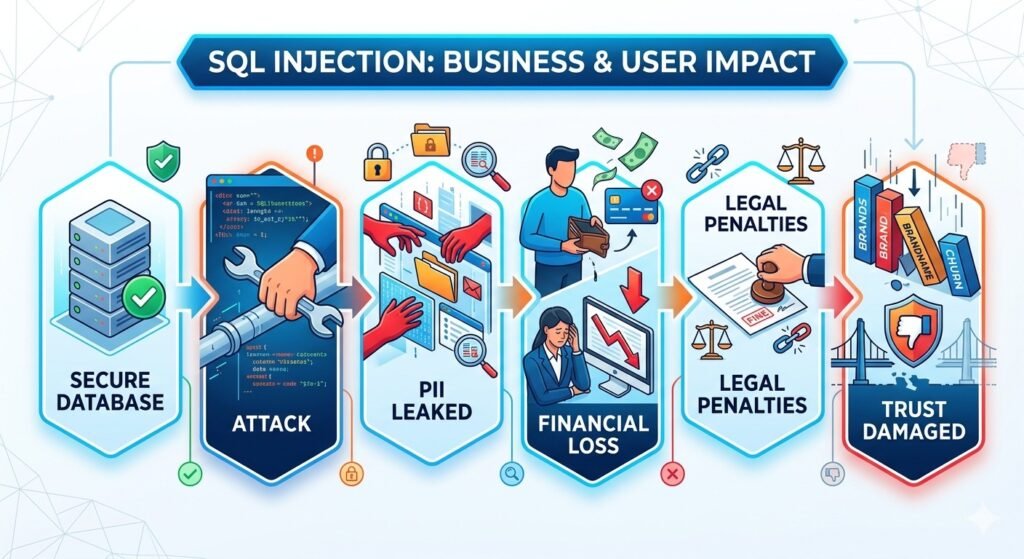
- Customer personally identifiable information (PII) gets exposed or sold on dark web markets
- Financial data including payment credentials becomes accessible to criminals
- Compliance violations under GDPR, HIPAA, or PCI-DSS result in regulatory fines
- Downtime caused by data wiping or ransomware deployment interrupts business operations
- Trust erosion leads to customer churn and long-term brand damage
Databases Most Frequently Targeted
While the core attack logic applies broadly, different database engines have unique quirks that attackers learn to exploit. Both MySQL and Microsoft SQL Server are prime targets due to their widespread deployment in web applications.
- Microsoft SQL Server is common in enterprise environments and supports dangerous extended stored procedures
- MySQL powers a significant share of open-source web platforms, making it a high-value target
- PostgreSQL offers stronger default security but is not immune when applications mishandle input
- SQLite is increasingly targeted in mobile and embedded applications
- Oracle databases remain vulnerable in large enterprise web portals
How Parameterized Queries Eliminate the Core Risk
The most effective technical defense against SQL injection attacks is the use of parameterized queries, also called prepared statements. This approach separates SQL code from user-supplied data entirely.
- The query structure is defined first, with placeholders for variables
- User input is passed separately and never interpreted as SQL syntax
- All major languages support prepared statements natively (PHP PDO, Java JDBC, Python psycopg2
- Stored procedures, when written correctly, offer similar protection
- PostgreSQL and MySQL both support parameterized queries at the driver level
Additional Layers of Defense Every Application Needs
Parameterized queries alone are essential but not sufficient. A layered security strategy reduces risk across multiple attack vectors.
- Input validation should reject unexpected characters and enforce strict data type rules
- Web Application Firewalls (WAFs) detect and block known injection patterns in transit
- Database privilege minimization ensures application accounts cannot access unrelated tables
- Error handling must suppress detailed database messages that leak structural information
- Security audits using tools like Burp Suite should be part of every development lifecycle
- Dependency scanning catches vulnerable third-party libraries before deployment
The Role of Security Testing in Prevention
Proactive testing is what separates organizations that catch vulnerabilities before attackers from those that discover breaches after the fact. OWASP provides detailed testing guides that development teams can follow systematically.
- Penetration testing simulates real attack scenarios against staging environments
- Static application security testing (SAST) analyzes source code for unsafe query construction
- Dynamic application security testing (DAST) tests running applications for injectable endpoints
- Bug bounty programs invite ethical researchers to report vulnerabilities responsibly
- Continuous integration pipelines can include automated security scans at each build
Developer Education as a Long-Term Solution
Technology alone cannot solve a problem rooted partly in human behavior. Developer training is one of the highest-return investments an organization can make in its security posture.
- Secure coding standards must be taught early in onboarding
- Code review processes should include mandatory checks for raw query construction
- OWASP’s free resources, including the Testing Guide and Cheat Sheet Series, provide practical references
- Developers who understand attack mechanics write significantly more resilient code
- Security champions within development teams create ongoing awareness culture
Conclusion
SQL injection attacks persist not because they are sophisticated, but because the conditions that enable them are still common. Unvalidated inputs, outdated codebases, and undertrained developers create opportunities that adversaries exploit daily. The technical solutions are well understood and widely available. Parameterized queries, proper error handling, privilege restriction, and regular testing through tools like Burp Suite eliminate the vast majority of risk. What is needed now is consistent implementation, organizational commitment, and a security-first mindset baked into every stage of the development lifecycle. The threat is not new, but the urgency to address it fully has never been greater.
Frequently Asked Questions
What are SQL injection attacks..?
SQL injection attacks are a type of cybersecurity exploit where malicious code is inserted into a database query through user input fields. This tricks the database into executing unintended commands, potentially exposing or corrupting stored data.
Why are SQL injection attacks still common in 2025?
They persist because many applications still use legacy code with unparameterized queries, developers sometimes lack secure coding training, and automated tools make it easy for attackers to scan large numbers of websites quickly.
How can I test my website for SQL injection vulnerabilities?
You can use tools like Burp Suite for dynamic testing, review your source code for raw SQL query construction, and follow OWASP’s Web Security Testing Guide for structured manual and automated assessment.
What databases are most at risk..?
MySQL, Microsoft SQL Server, and PostgreSQL are among the most frequently targeted because of their widespread use in web applications. However, any database engine is vulnerable if the application code fails to properly handle user input.
What is the best defense against SQL injection attacks..?
The most effective defense is using parameterized queries or prepared statements, which prevent user input from being interpreted as SQL code. This should be combined with input validation, WAFs, minimal database privileges, and regular security audits.
Does a Web Application Firewall fully protect against injection threats..?
A WAF adds an important layer of defense by filtering known attack patterns, but it should not replace secure coding practices. Attackers can sometimes bypass WAF rules with obfuscated payloads, so parameterized queries remain the foundational control.
